Arcane vs Dockhand: Which Docker Manager Should You Choose?
A hands-on comparison of Arcane and Dockhand, two new Docker management UIs. Licensing, features, security, and which one fits your setup.
Managing Docker containers doesn’t have to mean Portainer. For years, Portainer was the only serious web UI for Docker, and it worked fine until the licensing changes started pushing people toward paid tiers for basic features. That opened the door for alternatives, and two of them have been getting real attention lately: Arcane and Dockhand.
I deployed both on the same VPS running a mix of compose stacks. This comparison comes from actually using them, not from reading feature lists. Both are solid, but they target different users and make different trade-offs that matter.
Quick comparison
| Arcane | Dockhand | |
|---|---|---|
| License | BSD-3-Clause (fully open source) | BSL 1.1 (converts to Apache 2.0 in 2029) |
| Backend | Go | Bun + SvelteKit |
| Frontend | SvelteKit / TypeScript | SvelteKit 2 / Svelte 5 |
| GitHub stars | ~4.4k | ~2.4k |
| First release | 2022 | December 2025 |
| Contributors | 35 | 7 |
| Commits | 1,829 | 74 |
| Pricing | Free, always | Free (homelab), SMB $499/host/yr, Enterprise $1,499/host/yr |
| GitOps | Built-in | Git integration + webhooks |
| Vuln scanning | No | Yes (Grype/Trivy) |
| SSO/OIDC | Yes | Yes, free tier |
| CLI tool | Yes | No |
| Multi-env agent | arcane-headless | Hawser (NAT traversal) |
Architecture
These two took very different paths under the hood.
Arcane is written in Go. That matters because Go compiles to a single binary, so the whole thing runs lean. Memory footprint is small. The backend handles API requests, container management, and serves the SvelteKit frontend.
There’s a REST API you can hit directly, which is handy for scripting. Arcane also ships a CLI tool for people who want terminal access alongside the web UI.
For managing remote hosts, there’s arcane-headless, an agent you install on other machines. It connects back to your main instance.
Dockhand runs on Bun (not Node) with SvelteKit handling both the API routes and the frontend. The database is SQLite by default, with PostgreSQL as an option if you need it.
What’s unusual is the OS layer. Dockhand builds its container image from scratch using Wolfi packages via apko. No base image with leftover packages you don’t need. The attack surface is smaller because of this.
For remote hosts, there’s Hawser, an agent that handles NAT and firewall traversal. You don’t need to open ports on the remote machine.
My take on architecture
Here’s what each UI looks like in practice:
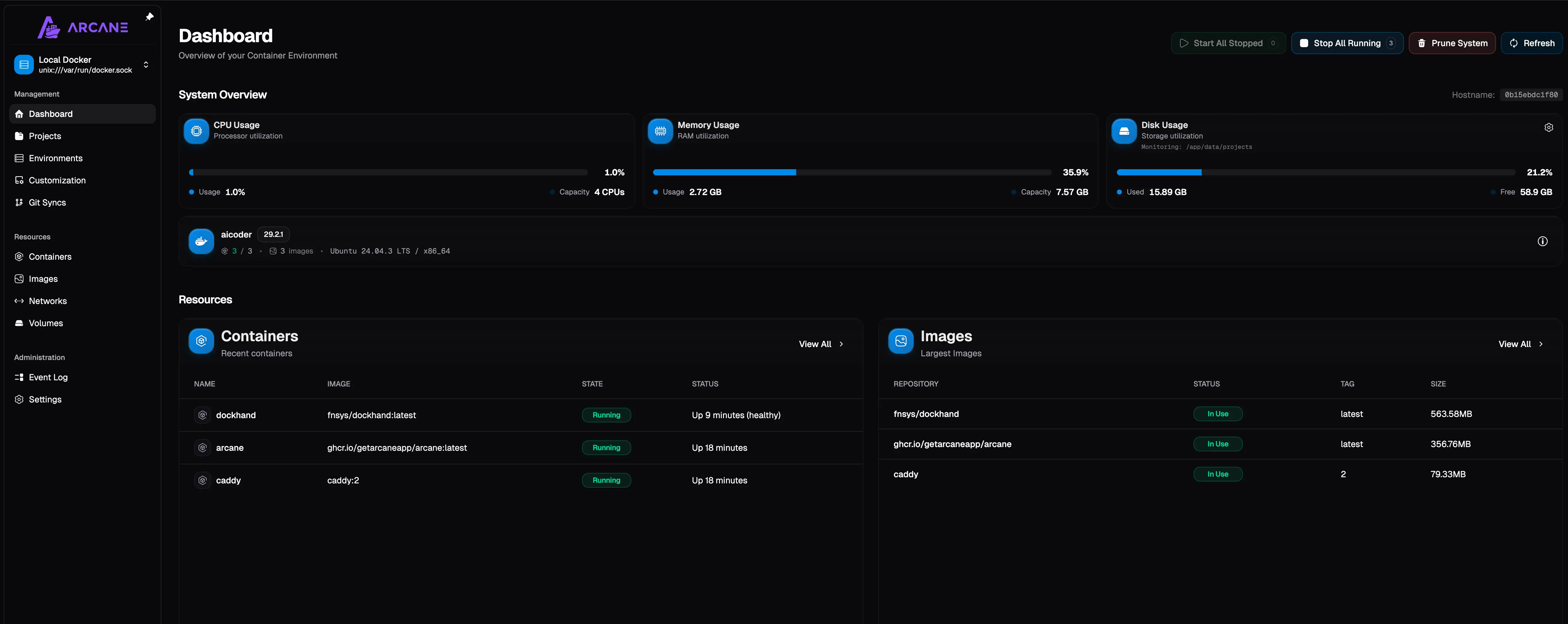
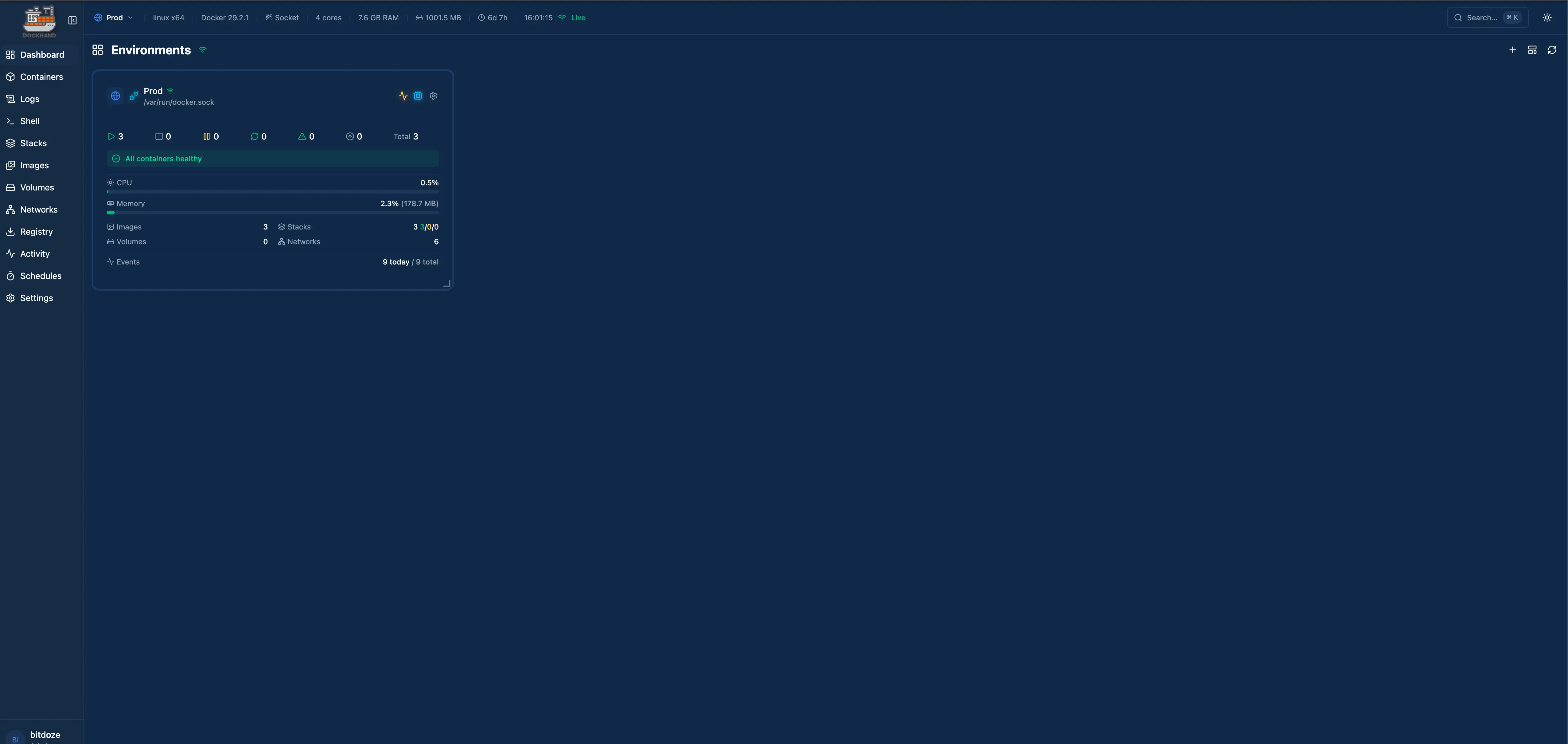
Arcane’s Go backend feels snappier for basic container operations. Page loads are fast, API responses come back quickly. Dockhand’s Bun-based stack is no slouch either, but you can feel the difference when clicking through lots of containers. It’s marginal, though. Both are faster than Portainer.
Licensing
This is where you really need to pay attention.
Licensing matters
Arcane is BSD-3-Clause. Fork it, modify it, use it commercially, sell it. No restrictions beyond keeping the copyright notice.
Dockhand uses BSL 1.1. You can use it freely for personal and internal business purposes. You cannot offer it as a commercial hosted service. The license converts to Apache 2.0 in 2029.
For most self-hosters, both licenses work fine. You’re running it on your own hardware for your own use. The BSL restriction on Dockhand only kicks in if you try to resell it as a service.
But if you’re building something on top of a Docker management UI, or you want to embed it in a product, Arcane gives you more freedom.
Features: where each one wins
Container and compose management
Both handle the basics well. You can start, stop, restart, and remove containers. You can view logs, inspect settings, and manage networks and volumes. Compose stack management works in both. You can deploy, update, and edit compose files from the web UI.
Where Arcane does it better
- The REST API is well-documented and easy to script against
- CLI tool gives you terminal access to everything the UI does
- GitOps is built in, not bolted on. Point it at a git repo and it syncs your stacks automatically
- SBOM (Software Bill of Materials) transparency for supply chain visibility
Where Dockhand does it better
- File browser inside containers. Browse the filesystem without exec-ing in
- Scheduled auto-updates with safe-pull protection (pulls new image, checks it works, rolls back if not)
- Activity logging for everything. You can see who did what and when
- Notifications via SMTP and Apprise (supports dozens of notification services)
Security features
This is where Dockhand pulls ahead.
- Dockhand includes vulnerability scanning with Grype and Trivy, built right into the UI
- OIDC/SSO is free in Dockhand, not locked behind a paid tier
- The custom Wolfi-based OS layer means fewer packages, fewer CVEs
- Zero telemetry. Dockhand doesn’t phone home at all
- Enterprise tier adds RBAC, LDAP, and audit logging
Arcane doesn’t have vulnerability scanning, though it does support OIDC/SSO. For a homelab, the security gap between these two is small. For a small business running production workloads, Dockhand’s built-in scanning and hardened OS layer are worth the trade-off of a more restrictive license.
GitOps and automation
GitOps is a first-class feature. You connect a git repository, and Arcane watches it for changes. When you push an updated compose file, Arcane pulls it and redeploys. No webhooks to configure, no external CI needed.
This works well if your workflow is already git-based. Push a change, see it deploy.
Git integration exists but works differently. You connect repos and set up webhooks. When a push happens, Dockhand receives the webhook and acts on it.
The scheduled auto-update feature is separate and arguably more practical for most people. Set a schedule, and Dockhand checks for new images, pulls them, verifies they work, and rolls back if something breaks. I’ve had it catch a bad image update twice already.
Multi-environment management
Both let you manage containers on remote hosts, but the mechanisms differ.
Arcane uses arcane-headless, a lightweight agent. Install it on a remote machine, point it at your main Arcane instance, and you can manage that host from the same dashboard.
Dockhand uses Hawser, which has a trick up its sleeve: NAT traversal. If your remote machine is behind a firewall or NAT, Hawser can still connect without opening ports. That’s genuinely useful for managing machines in different networks.
Maturity and stability
I have to be honest here. Arcane has a significant head start.
| Metric | Arcane | Dockhand |
|---|---|---|
| First release | 2022 | December 2025 |
| Total commits | 1,829 | 74 |
| Releases | 56 | 3 |
| Contributors | 35 | 7 |
Arcane has been around for years. It’s been through many release cycles, edge cases have been found and fixed, and there’s a real community around it. Dockhand shipped its first release two months ago. It’s polished for a v1, but it’s still a v1.
Stability in practice
I ran both for three weeks. Arcane didn’t crash once. Dockhand had one instance where the UI froze after a bulk container restart, and I had to refresh the page. Not a big deal, but worth mentioning.
Pricing
Arcane is free. No tiers, no paid features, no “community edition” with missing parts. BSD-3-Clause means you get everything.
Dockhand has a tiered model:
| Tier | Cost | What you get |
|---|---|---|
| Free | $0 | Full features for homelab use |
| SMB | $499/host/year | Commercial support, priority updates |
| Enterprise | $1,499/host/year | RBAC, LDAP, audit logging, dedicated support |
The free tier is genuinely usable. OIDC/SSO is included even at the free level, which is better than what Portainer offers. But if you need RBAC or LDAP, you’re paying enterprise prices.
Community and support
Arcane has the bigger community. More GitHub issues, more discussions, more people contributing. Thirty-five contributors versus seven tells you something about how many people are invested in each project.
Dockhand has gotten press coverage from XDA Developers, The New Stack, and Lawrence Systems. That’s impressive for a project that’s only been public for two months. But coverage and community are different things. When you hit a weird bug at 2am, the size of the community matters more than press mentions.
Both have active Discord/GitHub channels. Response times have been reasonable from both teams in my experience.
Installation
Both are Docker-based installs, which is appropriate for Docker management tools. I’ve written full install guides for both: install Arcane and install Dockhand.
Create a compose.yaml:
services:
arcane:
image: ghcr.io/getarcaneapp/arcane:latest
container_name: arcane
ports:
- "3552:3552"
volumes:
- /var/run/docker.sock:/var/run/docker.sock
- arcane-data:/app/data
- /opt/docker:/opt/docker
environment:
- APP_URL=http://localhost:3552
- PUID=1000
- PGID=1000
- ENCRYPTION_KEY=your-32-byte-encryption-key
- JWT_SECRET=your-jwt-secret
restart: unless-stopped
volumes:
arcane-data:Generate the secrets with:
docker run --rm ghcr.io/getarcaneapp/arcane:latest /app/arcane generate secretRun that twice - once for ENCRYPTION_KEY, once for JWT_SECRET. Then docker compose up -d and open localhost:3552. Default login is arcane / arcane-admin.
One thing to watch: if you want Arcane to manage existing compose projects, mount the projects folder with matching paths inside and outside the container. So if your stacks live at /opt/docker, mount it as /opt/docker:/opt/docker, not something like /opt/docker:/app/data/projects. Relative paths in compose files break otherwise.
services:
dockhand:
image: finsys/dockhand:latest
ports:
- "3000:3000"
volumes:
- /var/run/docker.sock:/var/run/docker.sock
- dockhand_data:/app/data
environment:
- SECRET_KEY=change-this-to-something-random
volumes:
dockhand_data:Also quick. Dockhand asks you to set a secret key, which is good practice. First-run setup walks you through creating an admin account.
Both require mounting the Docker socket, which is standard for these tools. If that makes you uncomfortable from a security perspective, both support connecting to remote Docker hosts instead.
Who should pick which
Pick Arcane if...
- You want something truly open source with no licensing concerns
- GitOps is part of your workflow
- You need a REST API or CLI tool
- Community size and project maturity matter to you
- Budget is zero, including for support
Pick Dockhand if...
- Security features like vulnerability scanning and SSO are requirements
- You manage hosts behind NATs and firewalls
- Auto-updates with rollback protection sound appealing
- You want activity logging and audit trails
- You’re okay with a newer project that’s still finding its footing
My honest take
If someone asked me which one to install today on a homelab server, I’d say Arcane. It’s more mature, fully open source, and the GitOps integration is excellent. The community is bigger, so when things go wrong, you’ll find help faster.
But I’m watching Dockhand closely. The security features are ahead of anything else in this space at the free tier. OIDC without paying, vulnerability scanning built in, that hardened OS layer. If the team keeps shipping at this pace, and if the project grows its contributor base, it could become the better choice for production use within a year.
For now, Arcane for reliability. Dockhand if you need those security features and can tolerate some rough edges. And if you want something that tries to be the full package, with container management, backups, reverse proxy, monitoring, and multi-node all in one tool, check out UsulNet.
Related articles
- Best Portainer alternatives in 2026 - five Docker management UIs compared
- Install Arcane - full Arcane setup guide with socket proxy and OIDC
- Install Dockhand - full Dockhand setup guide with vulnerability scanning and Hawser
- Install UsulNet - all-in-one Docker management platform with scanning, backups, and multi-node
- Install Dockge - another Docker management UI worth trying
- Best Docker containers for home server - what to run once you’ve picked a manager
- Best self-hosted panels - server management panels compared
- Podman vs Docker - the container engine comparison
- Docker auto-update with Tugtainer - keep containers updated automatically
- Server monitoring tools - monitoring your Docker host

